In our previous interview with Darin Andrew, Senior PKI Architect at DigiCert, we discussed the differences between public and private PKI. We established that most enterprises use a hybrid PKI solution.
That said, you have two options for implementing your private PKI: (1) use a hosted solution from a certificate authority (CA) or (2) build your own internal CA. Because people often wonder about the costs and benefits of each, we asked Darin to break them down for us.
Let’s say I’ve decided to create a private root—should I use a hosted or internal CA?
DA:
It’s possible to set up your own internal CA. The real question is, does it make sense for your organization to put the resources into building that internal CA? This has to be looked at on a case-by-case basis.
The goals of the average company don’t revolve around creating a robust PKI solution. If you’re a commercial CA, that’s your number-one goal. But engineers in most companies have more immediate goals, like keeping their sales force or manufacturing lines going.
Often, a hosted solution can give you everything you need. Then, your engineering team can focus on your organization’s most critical projects. For some companies, it makes sense to build an internal CA. Unfortunately, I often see companies building internal CAs not because it’s what’s best for their company, but because they have misconceptions about hosted solutions.
What are some of those misconceptions about hosted solutions?
DA:
In short, the common misconceptions revolve around cost, capability, and flexibility.
Many have only dealt with a CA to purchase publicly trusted SSL certificates for their web pages. Because this is their only reference point, they assume private certificates will have the same per-cert costs as publicly trusted certificates—this isn’t the case.
Issuing a private certificate with a hosted CA is usually a fraction of the cost of a publicly trusted certificate with that same CA. We almost always get the per-cert cost for private certificates below what our customers were projecting.
Another common misconception many have is that they won’t be able to accomplish the same goals with a hosted solution. For example, you might wonder whether you can automate certificate issuance with a hosted solution. Many commercial CAs have tools, like APIs, for automating certificate management. Before you choose a commercial CA, check out their platform and tools.
Many also think a hosted CA will limit them to certain certificate profiles. They think they’ll only get certificate profiles that are approved by the CA/Browser Forum. Because these are private certificates we’re talking about, DigiCert will provide any certificate profile you need. They don’t have to be SSL certificate profiles. They don’t even have to be X.509.
So, how do I decide if it makes sense for my organization to build an internal CA?
DA:
The first thing to consider is scale. How do you determine the scale of your PKI?
In our first interview, we talked about looking 5 to 10 years into the future. Companies often build an internal CA based on today’s needs, only to find that it’s not sufficient for tomorrow’s needs.
For example, let’s say your current need for an internal CA is to issue authentication certs to your laptops and phones, so they can authenticate into your wireless.
Five months down the road, you might realize you need to set up certs for all your internal servers. You might want certificates to be issued to all servers automatically through an API.
Now, you’re creating an API interface, which is yet another project. What started as a small project is now ballooning into a resource-intensive one.
Don’t be fooled by the scope of the project today—think long term. It’s hard to guess what you’ll need 5 to 10 years from now. An established commercial CA is a good resource for this because it has worked with a broad range of enterprises. A commercial CA has a view into how those PKIs have scaled over the years.
What are some of the costs of creating an internal CA?
DA:
Often I see that the cost of personnel is left out of creating an internal CA. I’m not just referring to the cost of hiring additional personnel to build and manage the internal CA, but also the opportunity cost of your engineering team’s time.
Your engineering team likely has a bunch of other responsibilities for security and maintaining infrastructure. Things like email servers, wireless, penetration testing, audits, risk assessments, and the list goes on. They have a lot on their plates. Creating an internal CA could take them away from other important tasks.
Another thing people forget is that issuance is only one piece of the puzzle. It’s great to keep in mind other crucial pieces, like revocation.
Look, you could end up spending half a million dollars to build an internal CA, but it really depends on the scope and scale of your project and your projected future needs. For the goals of some companies, it could cost less or more.
Instead of putting dollar amounts on the costs, it probably makes more sense just to list out the items to consider. There’s just no way to put a dollar amount to it, because there’s so much variation from company to company. That said, the following list will help you by identifying whether you need each line item and evaluating the cost of each for your business.
Darin broke down the cost considerations for us during the interview. They break down into six main categories:
- Hardware, software, and licensing
- PKI expertise
- Training
- Certificate policy (CP) and certificate practices statement (CPS)
- Auditing against certificate policy
- Vulnerability testing
For the purposes of this post, we will focus on hardware, software, licensing, and personnel. Here’s a more detailed look at what those costs include in each category:
Hardware, Software, & Licensing
- CA server including redundant CA server
- Online Certificate Status Protocol (OCSP) and Certificate Revocation List (CRL) distributed services for redundancy and high availability, as well as fast response times
- Firewalls, segregated networks, and dedicated rack space
- Storage mechanism for offline root and backup of offline root—HSMs required
- Signing HSMs
Personnel
- PKI authorities and administrators
- Developer resources to write interface used to request/revoke certs (if needed)
- Audit staff
- Regular training of staff who have PKI responsibilities (certifications, conferences, etc.)
Note: Avg. industry salary: $120-$200k per individual
DA:
Of course, these aren’t all the possible cost considerations, but we’ve given you some of the key costs to get you started. The best thing you can do in this position is reach out to a PKI engineer at an established commercial CA. They will help you evaluate your specific PKI architecture needs, which will give you a detailed and accurate cost projection.
If you’re considering a hosted solution, make sure the commercial CA you’ve chosen can give you the customization you need.
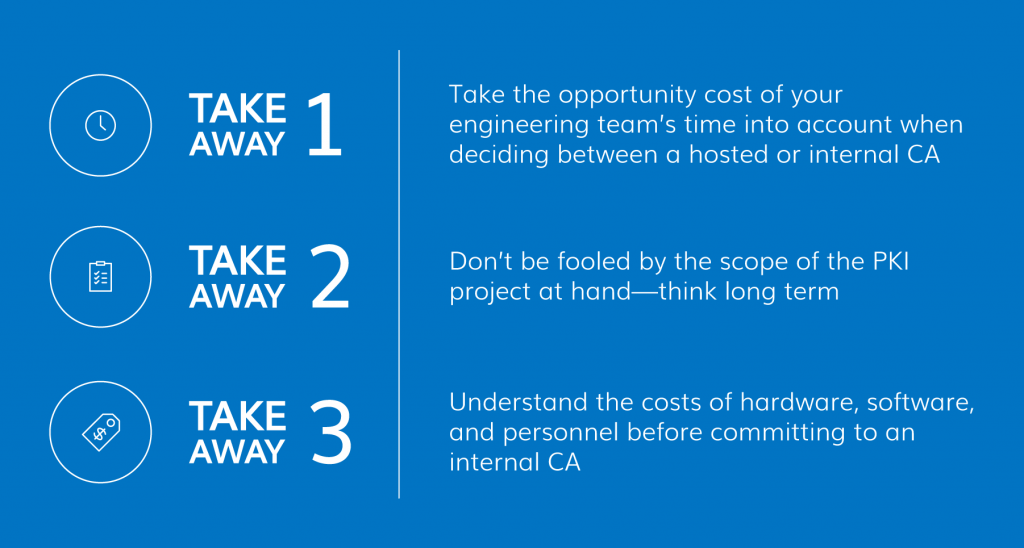
In our next post, we’ll tackle how to automate certificate management. For now, here are your takeaways: