After years of warnings and predictions, we’re entering an era in which you can begin to deploy post-quantum cryptography (PQC) on your own systems. We know our customers want to get started on the post-quantum journey, so we’ve created a simple, fully PQC-protected web application and published it in a GitHub repository.
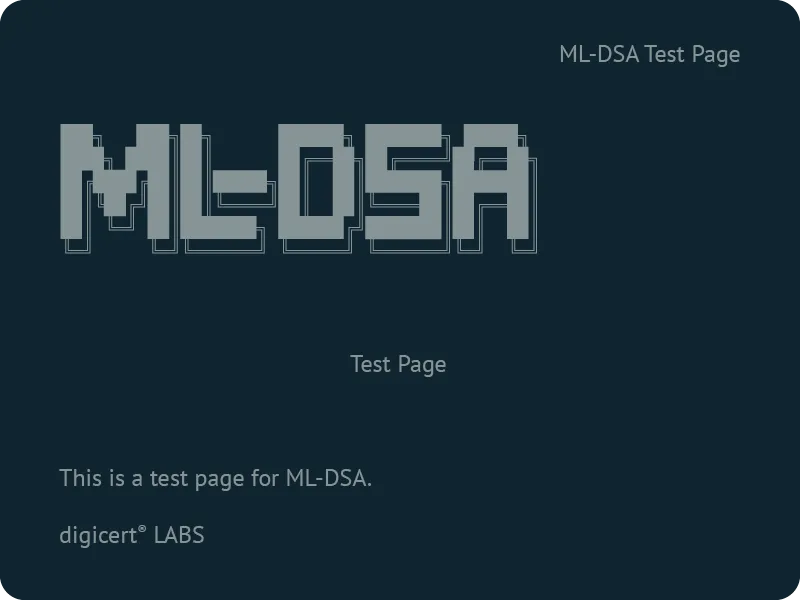
The application is simple. It generates a banner page to confirm successful execution. But the page is retrieved over HTTPS. The TLS certificate for the page uses ML-DSA as the digital signature algorithm. ML-DSA is a quantum-safe algorithm intended (eventually) to replace RSA and ECDSA. This makes it a true post-quantum application.
Implementing the application will require Linux administration skills. The instructions are written to run it on an Amazon Web Services account, but using another cloud or a self-hosted system could work. The remaining software (Nginx, OpenSSL client, Curl and/or Links) is open-source and downloadable. If you have the experience, you may be able to migrate it to other Linux environments and web servers, and congratulations if you do. Please let us know at pqc.labs@digicert.com.
You won’t use a web browser as the application's client because none of them support ML-DSA yet. We have tested it with Curl, a command-line tool that retrieves and displays raw HTML, and Links, another command-line tool that generates a text rendering of the page. Here is the output in Links:
`



