See the Power—and Promise—of Digital Trust in the Real World
Learn how DigiCert is leveraging new solutions to extend trust further than ever before.
Download the ebook and Learn How to Improve
your Security Posture with Digital Trust
Learn more about digital trust for the real world.
What’s the Difference Between a
Buzzword and a Business Imperative?
Real-world results.
What is digital trust? And, more importantly, what does it mean for you, your organization and the greater world we live in?
Download the DigiCert eBook, “Digital Trust for the Real World,” to learn why digital trust has become an operational imperative and how companies are embracing and extending trust to achieve real-world results—from the Alaskan frontier to the edge of space.
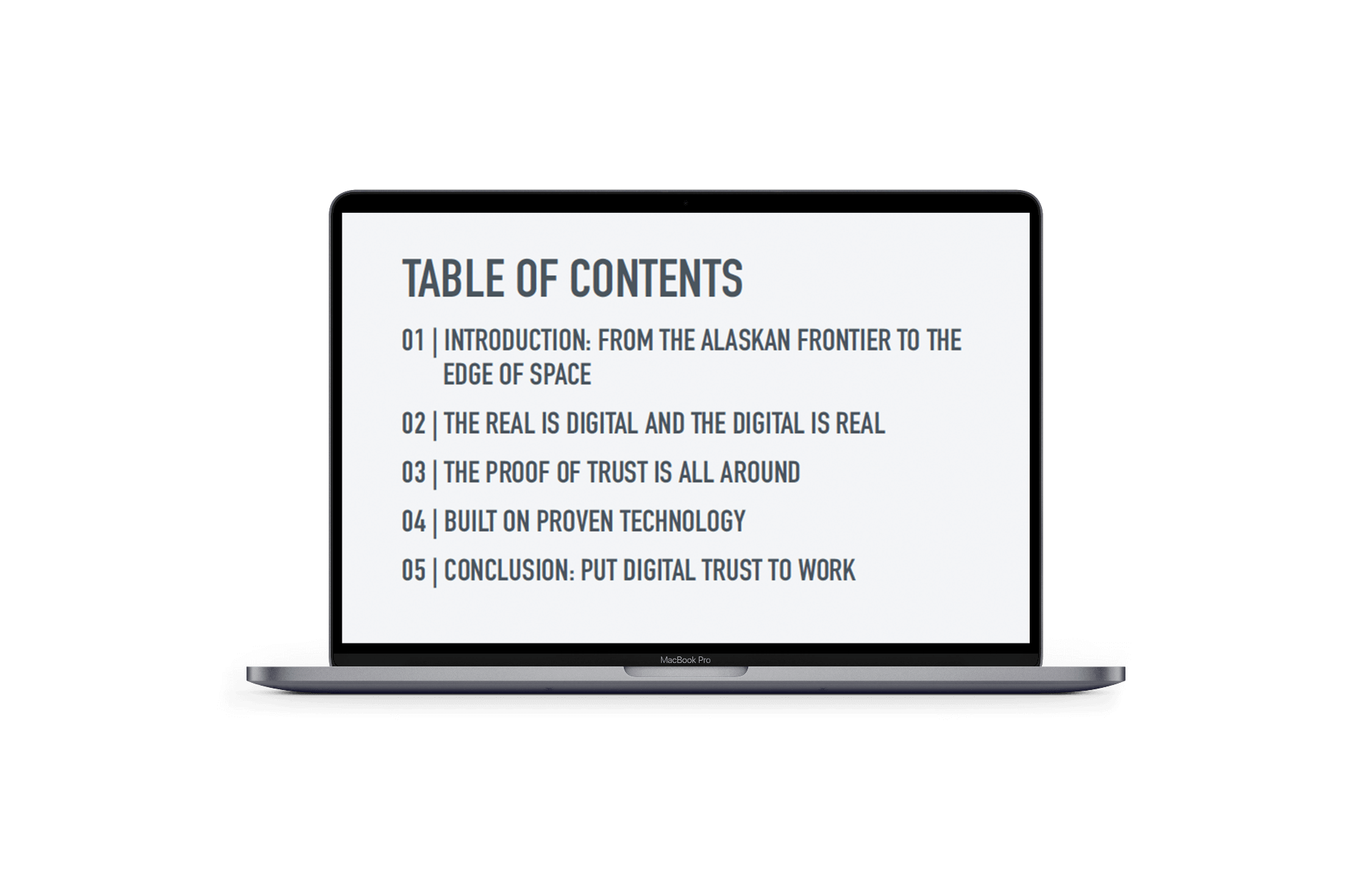
Here’s what’s inside: