Insights: Digital Trust
Digital Trust for
the Real World
Everything is connected, everywhere—so traditional boundaries no longer apply. See the CUBE.net interview about the secure foundation for our new, borderless reality.
Today, the digital is real and real is digital. Machines are the internet, the internet is apps, apps are made up of user data interfacing with networks. Today, workouts are data points, TV shows are streaming content, mobile phones run office meetings. The lines between personal and work are blurring.
This is a world where traditional terms, definitions, and modes of operating no longer apply to how and what we connect—which means traditional modes of security no longer apply. This new world needs more than just software and solutions. It needs digital trust.
years’ worth of content streamed in 2021

connected endpoints in 2021

of data produced annually by 2025
Optional heading that can be visually hidden
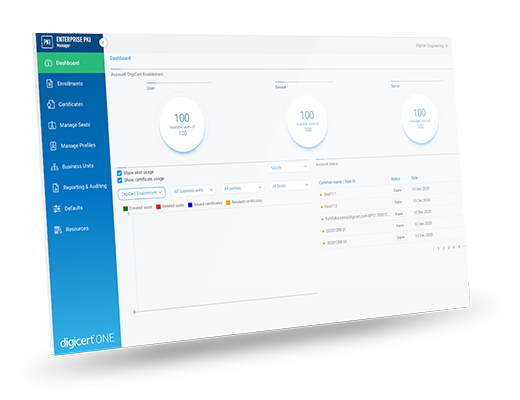
See Digital Trust at Work
Want to learn more about how digital trust is transforming day-to-day business for companies around the globe?
Download the new eBook today to learn:
- What digital trust is—and why it matters
- The technological foundation you need to achieve real-world results
- How companies are realizing digital trust from the Alaskan frontier to the edge of space

What Is Digital Trust?
As opposed to a single-use security application, digital trust is a complete architecture, made of practices, tools, systems and organizations that collectively protect an entire ecosystem—regardless of its size, use, or lack of easily defined boundary. With digital trust, businesses, governments, consortia, and individuals can confidently engage with a secure digital world. The four key elements of digital trust:

Digital Trust Deep Dive
Lisa Martin of theCUBE.net and Dr. Amit Sinha break down how digital trust is at work today enabling everything in our connected reality—users to servers, software to content, documents to devices, and more.
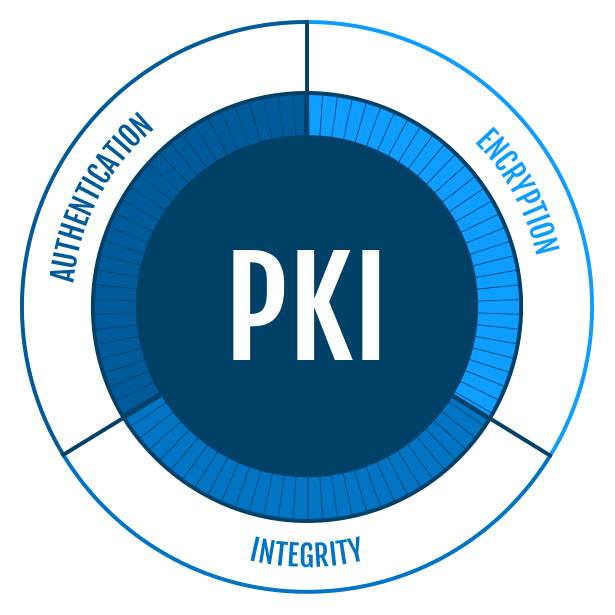
PKI—a Foundation of Digital Trust
Public Key Infrastructure binds cryptographic public-private keys to identity using certificates attached to digital objects—like websites, emails, networks, software and users. Trusted for decades, PKI is proven security technology. Because digital trust relies on authentication, integrity and identity for deployment and operation, PKI is the perfect vehicle for delivering trust to people, systems and organizations.
Identity
Individuals, businesses, machines, workloads, containers, services, and anything else that connects must be authenticated with a cryptographically unique identity.
Integrity
Objects must be used and transmitted with tamper prevention, as well as tools for verifying that object hasn’t been altered.
Encryption
Data must be secured in transit.
The Responsibility of Security Professionals
Companies are the stewards of digital trust not only for their own internal employees and operations, but also for their customers, partners and extended communities. Vulnerabilities can no longer be viewed as isolated concerns in this new borderless world. Which is why security professionals must deploy software solutions and best practices that deliver digital trust to everything that connects—all the way to the edge.
Related Resources

REPORT
State of Digital Trust
WHITEPAPEr
Digital Trust: The Foundation for Digital Freedom

BLOG POST
Digital Trust for the Perimeter-less Enterprise
