Certificate lifecycle management reaches an inflection point
What used to be a background security function is now a visible source of operational risk. Shorter TLS lifecycles and rapidly growing certificate volumes are forcing organizations to rethink how certificates are managed—at scale, across systems, and without failure.
This isn’t a gradual shift. It’s an operational inflection point.
Certificate lifecycle management (CLM) now directly impacts uptime, security posture, and an organization’s ability to adapt to change.
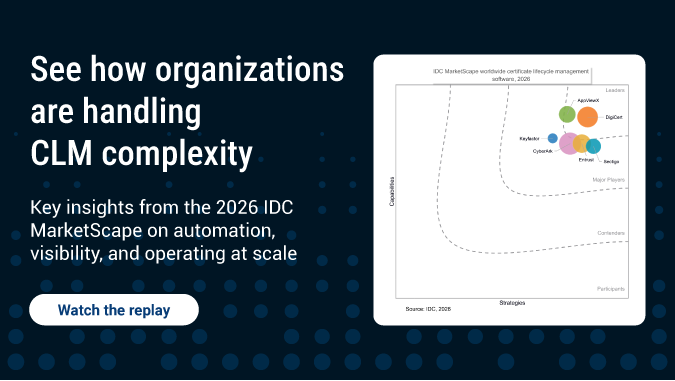
Industry analysis, including the 2026 IDC MarketScape for CLM, reflects this shift as organizations move away from fragmented, manual approaches toward scalable lifecycle management strategies.
Lifecycle compression is reshaping operations
TLS certificate validity periods have steadily decreased, with further reductions already on the calendar. As lifecycles shrink, the number of required renewals increases accordingly.
A certificate that was once renewed annually may now require multiple renewals over the same period. This change doesn't just increase activity—it fundamentally alters how certificate management operates.
Teams are now handling a higher volume of renewals with less time to execute each one. At the same time, each renewal often depends on coordination across systems that don't behave consistently, from cloud workloads to legacy infrastructure.
This combination introduces a new kind of pressure. Execution windows are tighter, dependencies are more complex, and failure tolerance is lower.
Under these conditions, manual processes begin to break down. Delayed approvals, missed notifications, or inconsistent deployment steps are no longer edge cases—they’re common failure points.
The real challenge is continuous management
Most certificate-related outages stem from gaps in visibility, unclear ownership, or inconsistent renewal processes. These issues become more pronounced as environments grow more distributed.
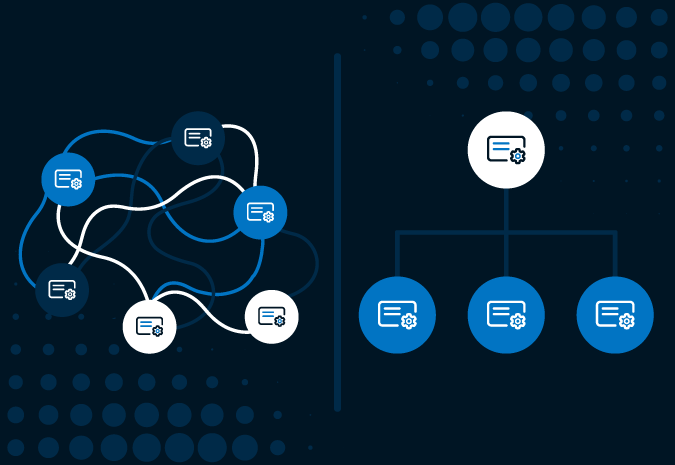
Certificates now span cloud platforms, on-premises systems, network devices, and internal services. Ownership is often fragmented across teams, and workflows vary depending on the system or tool in use.
This fragmentation introduces risk that’s difficult to detect and harder to control. Without centralized lifecycle management, complexity compounds quickly.
Automation is now a baseline requirement
Many organizations operate in a hybrid state, combining partial automation with manual approvals and system-specific workarounds. While this may function at smaller scale, it introduces fragility as certificate volumes and renewal frequency increase.
Automation must extend beyond isolated scripts or narrow use cases. It needs to operate consistently across environments and integrate into existing operational workflows.
To be effective, lifecycle automation must provide:
- Complete visibility into the certificate estate
- Consistent execution across different systems
- Centralized policy enforcement and governance
- Support for multiple certificate authorities and certificate types
These are no longer advanced capabilities. They're the baseline for maintaining operational control.
What this inflection point means
Organizations are being asked to manage shorter lifecycles without increasing outages, apply automation across heterogeneous environments, and maintain continuous visibility into their certificate estate, all while preparing for ongoing cryptographic change.
As post-quantum cryptography (PQC) moves from future concern to active planning priority, the ability to discover, manage, and update certificates at scale becomes even more critical. The same gaps that create risk under shorter lifecycles—limited visibility, inconsistent automation, fragmented control—also make large-scale cryptographic transitions difficult to execute.
This represents a shift from reactive certificate management to continuous lifecycle operations. Industry recognition, including DigiCert’s position as a Leader in the 2026 IDC MarketScape for CLM, reflects the growing importance of platforms that can support this transition at scale.
How to operationalize certificate lifecycle management
The first step is establishing complete visibility. Organizations need to identify where certificates exist, who owns them, and how they’re managed across environments.
From there, the focus shifts to applying automation consistently. Lifecycle processes such as renewal, deployment, and revocation must operate reliably across all systems, not just those that are easiest to integrate.
Finally, organizations need to be building for adaptability. Lifecycle requirements will continue to evolve as certificate lifespans change and new cryptographic standards emerge. Systems have to be flexible enough to support different environments, certificate types, and operational models.
These priorities are interconnected: Visibility enables automation, which enables adaptability. Together, they form the foundation for managing both current lifecycle demands and future change.
See how organizations are adapting in practice
The move to continuous certificate lifecycle management raises practical questions around automation, visibility, and managing complexity across environments.
These challenges—and how organizations are addressing them—are explored in more detail in the IDC MarketScape discussion with IDC Research Director Jennifer Glenn.
Watch the webinar replay to see how security leaders are approaching certificate lifecycle management at scale.