Firefox 32 Supports Public Key Pinning

On September 2, Mozilla launched Firefox 32 for Windows, Mac, Linux, and Android. This new version of Firefox includes support for Public Key Pinning (PKP), adding another layer of security for Firefox users by ensuring they connect to their intended site.
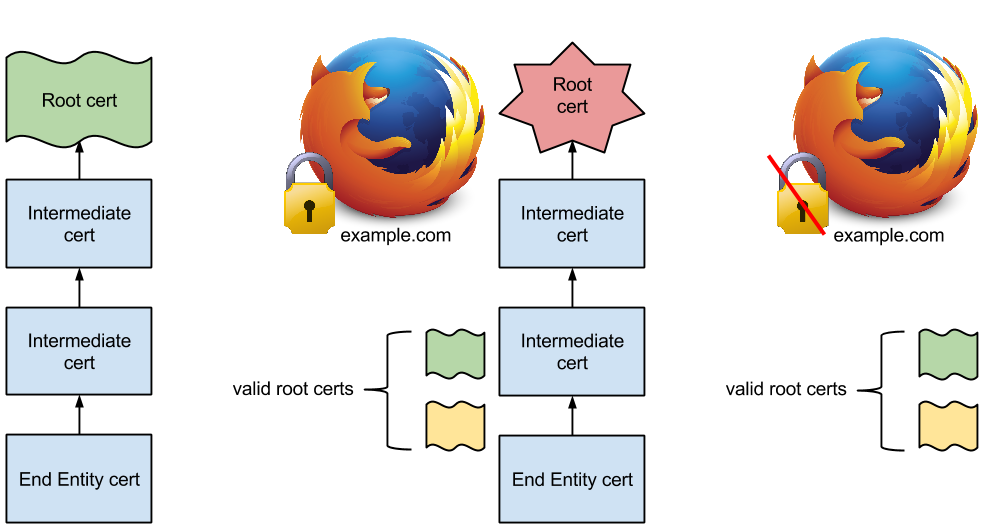
PKP is a way for sites to indicate which Certificate Authorities (CAs) have issued valid certificates for their site, and PKP also rejects certificates that do not match the pinned and trusted CAs. Using PKP helps guard users against man-in-the-middle attacks by rejecting certificates issued by rogue CAs not pinned by the site.
When users visit a site that is pinned, the lock icon will appear as it normally would. However, if a user visits a site that has a root certificate that has been pinned and the certificate for that site does not match the pinned CA’s root certificate, Firefox will not allow the connection. By using PKP the chances of visiting a spoofed site and becoming prey to a man-in-the-middle attack are minimized. Pinning errors will also display if a certificate has been mis-issued.
Some users have seen a message that a secure connection failed while trying to connect to a pinned site in Firefox over WiFi. However, this error should disappear if the user sets up WiFi access and then refreshes the page.
Firefox 32+ will support built-in pins and pinning will be enforced by default. Sites will have the option of advertising their support for pinning with the PKP Extension for HTTP, which Firefox will make available in the near future. Domains that are already pinned are addons.mozilla.org, Twitter, and Google and more sites are being added. If you are unsure which domains have been pinned or you would just like to browse which ones are pinned, you can visit the Public Key Pinning wiki.




