Helping Users Avoid Account Takeover
How Verified Mark Certificates help reduce risk and protect
your brand
The cliché in security is that users are the weakest link. What if they aren’t? What if this last mile in the fight against account takeover and malware is vigilant and increasingly resistant to scams?
Account takeover fraud is a massive source of losses for e-commerce businesses and retail banks. According to the 2022 Identity Fraud Study by Javelin Strategy & Research, losses from account takeover totaled $11.4B, an increase of 90% over the previous year. To combat this type of attack, large retailers and banks have implemented Domain-based Message Authentication Reporting and Compliance (DMARC) to make it harder for cybercriminals to impersonate their brands.
However, DMARC is not visible to users which makes it difficult for them to know if an email sender is authentic. Users often make split-second judgments to trust an email or delete it based on their initial impressions. When these authentication protocols are not visible, recipients lack the immediate reassurance needed to distinguish legitimate emails from phishing attempts or spam, leading to missed business opportunities and potential security compromises.
To help recipients distinguish authentic from impersonated senders, mailbox providers like Gmail and Apple have implemented the ability to trigger the display the logo of the email sender in the recipient’s mailbox if the email has passed various authentication checks. The technical name for this is Brand Indicators for Message Identification (BIMI) and it provides users with instant visual cues regarding the authenticity of an email. In turn, users are less likely to click a malicious link, open a malicious attachment or otherwise engage with bad actors. They can make better security decisions, faster.
Let’s examine two separate emails to better understand how DMARC and brand indicators help fight account takeover.
A tale of two emails
Both emails were delivered to my junk folder: one is malicious, one is not. As I mentioned above, there are no visual indicators that I can use to instantly tell the authentic email from the spoofed one. In fact, I initially thought the Amazon email was a scam because I wasn’t expecting it and the email domain looks odd to me. I knew the Facebook email was a scam because I don’t have a Facebook account.
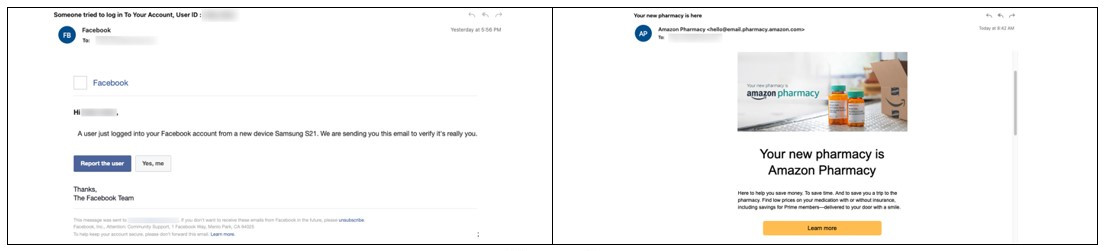
Figure 1
Pass-fail authentication tests
To view the results of sender authentication tests performed by receiving servers I needed to analyze the email headers. Email headers are akin to detailed tracking information for a package. The headers contain information about the email sender, how the email was routed and the results of authentication checks along the way.
None of the above
The email authentication checks associated with DMARC are thought of as being Pass or Fail but they are Pass, Fail or None.
Here are the related parts of the email header for the fake Facebook email:
- sender IP is 89[.]144[.]9[.]88
- smtp.mailfrom=inlkrqa.co.uk
- inlkrqa.co.uk does not designate permitted sender hosts
- dkim=none (message not signed)
In the case of the fake Facebook email, the message was sent from a nonexistent domain, which explains why the domain owner doesn’t designate permitted senders. No domain means no authentication records for mailbox providers to use for verifying the sender. As I mentioned earlier, none of this information is readily viewable by the recipients.
Nothing's ever easy
Here are the related parts of the email header for the seemingly legitimate Amazon email:
- sender IP is 13[.]110[.]209[.]206
- smtp.mailfrom=bounce.email.pharmacy.amazon.com
- bounce.email.pharmacy.amazon.com designates 13.110.209.206 as permitted sender
- dkim=pass (signature was verified)
Now we know the Amazon-looking email came from an email server that’s been properly configured to send messages on behalf of bounce.email.pharmacy.amazon.com. That domain name is long, and I’ve learned not to trust my eyes when it comes to spotting look-alike domains because of Punycode.
I checked the Sender IP address and it’s owned by Salesforce, not Amazon. It’s reasonable to assume that Amazon sent this email from their customer marketing platform hosted by Salesforce. I don’t know if this is a shared IP address, so I was still skeptical because Salesforce is a shared platform. Finally, I used “whois” to lookup the owner of the sender domain, who turns out to be Amazon Technologies, Inc.
I’m still not going to click any links. My initial suspicions about the trustworthiness of this email created a lasting skepticism. And this was after digging into all the technical details. I usually decide to read or delete an email in less than 5 seconds. That decision includes the time for me to decide if I’m interested in the content and if I trust it enough to click the call to action.
The last mile
Obviously, a typical customer won’t do this much investigation to decide whether to trust the sender of an email. That leaves them with two options: click the link and hope for the best or delete the email and move on. Obviously, neither are ideal outcomes for businesses trying to engage their customers and simultaneously help them avoid scams. BIMI can help.
BIMI enables visual cues of email authenticity that make it easier for users to trust your emails and make it harder for criminals to impersonate your brand. This not only means users are less likely to fall victim to email-borne attacks, but they are also more likely to engage with your emails. It’s human nature to gravitate towards the things we trust.
Compare the two emails below. Which one would you trust? Notice the Amazon logo next to the sender’s name, the checkmark and the mouseover text that explains Amazon has proven ownership of the domain and logo.
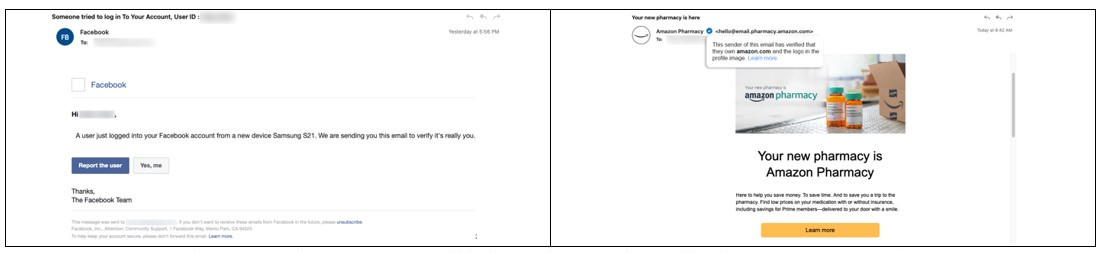
NOTE: Amazon Pharmacy has BIMI enabled. Kudos to them for being proactive!
Trusting trust
If BIMI is intended to convey trust of the sender, why should you trust BIMI?
BIMI is enabled by a combination of DMARC and Verified Mark Certificates (VMCs). DMARC allows the owner of a domain to publish a policy for how receiving email servers should handle messages that cannot be authenticated to the domain — reject, quarantine or none. Mailbox providers want domain owners to enable DMARC enforcement (read: reject or quarantine) because it allows the providers to have “cleaner pipes” by rejecting inbound messages that fail authentication checks.
VMCs are public trust certificates available from DigiCert. For a domain owner to receive a VMC, their organization must successfully pass a validation process that includes verifying ownership of the domain and trademark — much like amazon.com uses a web server certificate to prove authenticity of the site.
Of course, a cybercriminal could create a business entity, purchase a domain, properly configure the SPF/DKIM/DMARC records for that domain, register a trademark and go through the validation process to receive a VMC. That’s not likely to happen because criminals want to make a fast buck without exposing their identities. Also, the validation process to get a VMC makes it extremely difficult to impersonate a brand.
Enable and engage your customers
Account takeover fraud is a top concern for retail banks and online retailers. Many of them are enforcing DMARC to protect their brands from impersonation attacks. However, consumers still fall victim to phishing and malware attacks that leak their credentials. BIMI and VMCs provide businesses a way to protect their customers by enabling consumers to visually verify messages from trusted email senders. It’s an action with a double bottom line — financial profit and social responsibility. If your organization hasn’t enabled BIMI or hasn’t started the process, now is the time to get moving. Check out our FAQ to learn more.




