
Complimentary research
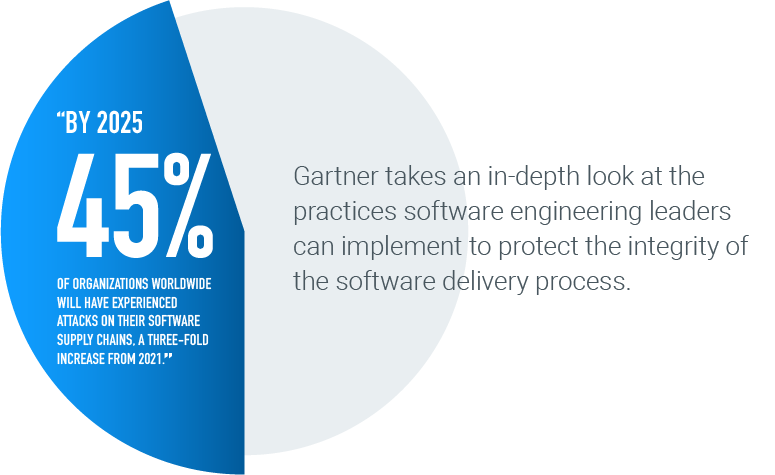
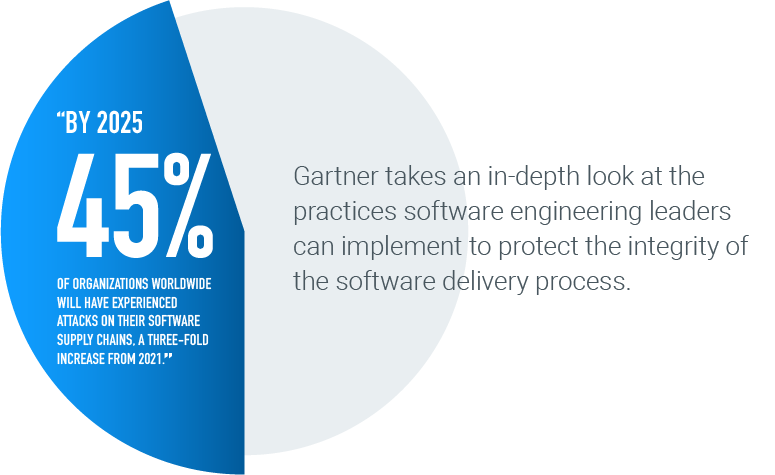
How Software Engineering Leaders Can Mitigate Software Supply Chain Security Risks
Explore potential software supply chain security risks and the strategies software engineering teams can use to counter them.
Optional heading that can be visually hidden
Read the Report to Learn About:
How Software Engineering Leaders Can Mitigate Software Supply Chain Security Risks. By Manjunath Bhat, Dale Gardner, Mark Horvath. Published 15 July 2021. Refreshed 22 November 2022.
GARTNER is a registered trademark and service mark of Gartner, Inc., and/or its affiliates and is used herein with permission. All rights reserved. Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.





