DigiCert® Device Trust Manager for Home and Consumer
Proven IoT Security for Home & Consumer Devices
Smart security to protect private data and guard
against unauthorized access for home and consumer
IoT devices. That’s digital trust for the real world.

If It’s Connected, It Needs IoT Trust
Recent studies have shown more than half of consumers—even those who have owned smart devices for years—don't trust the security of their IoT devices.
DigiCert works with manufacturers to build IoT trust into devices, so security becomes a part of the device’s DNA. Silicon injection to sunset, PKI delivers trusted security and identity solutions that work everywhere—from routers to refrigerators and smart watches to 5G. It's confidence your customers will want to take home.

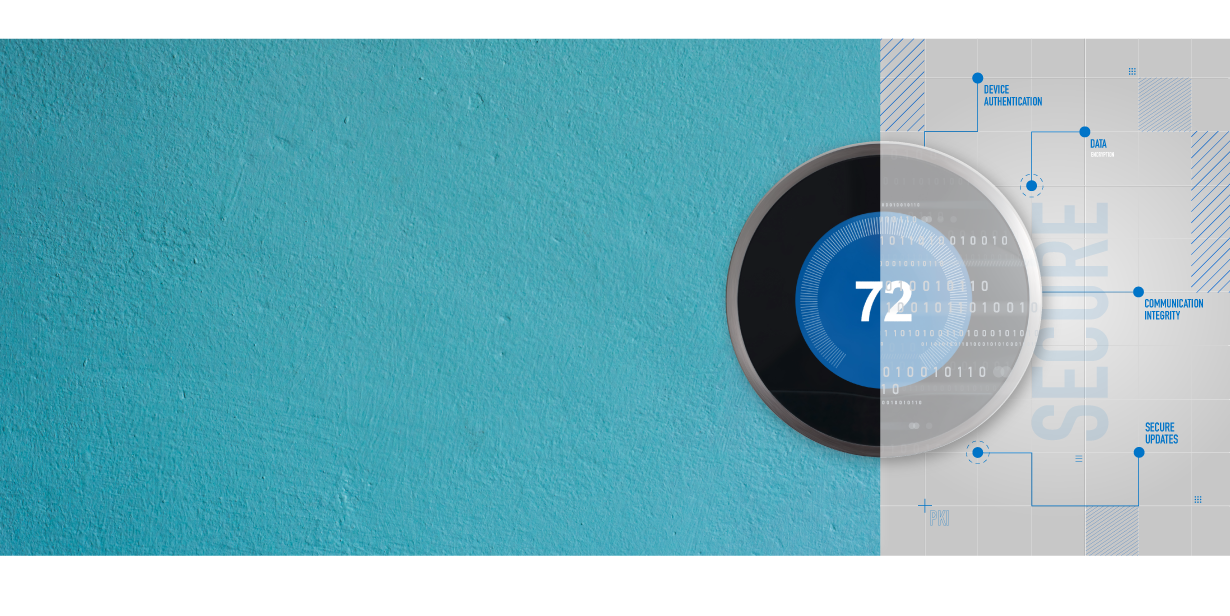
360-Degree Protection for All Your Gadgets and Tools
Public Key Infrastructure (PKI) uses digital certificates to verify the identity of connected devices, keeping information private while ensuring the integrity of the code. No matter how you look at it, DigiCert Device Trust Manager has you covered.
- Authentication
- Certificates for devices validate identities to ensure only authorized users, messages, or other types of servers have access to the device.
- Encryption
- A certificate creates an encrypted link and allows information to be transmitted privately.
- Integrity
- Certificates make sure there’s no alteration to messages or data transferred between devices.

Matter Smart Home Standard
Matter provides smart home devices with interoperability, reliability, ease-of-use, and robust security. This universal standard enables any universal communication between any Matter-compliant device on any platform or ecosystem, including Google Home, Amazon Alexa and Apple HomeKit. To meet the standard for Matter, you’ll need to secure your IoT products using Device Attestation Certificates (DAC).
Quality and Control
Related Resources

WEBINAR
Matter Compliance: Understanding and Implementing Device Attestation Certificates
DATASHEET
DigiCert for Connected Devices

DATASHEET
DigiCert IoT Trust Manager

A Foundation for Digital Trust
DigiCert ONE is more than just a platform. It’s a new way of thinking about how you secure and manage everything of value in your organization. From the individual website to the massive enterprise, DigiCert ONE makes security, validation and identity powerful and easy. No matter the size or use, DigiCert ONE delivers control and simplicity for the highest level of assurance.
